Phishing continues because unfortunately it works. This article provides a good overview of some of the basic techniques in play at present. A lot of these attacks are simply modern versions of age old scams run by con artists for many decades. Instead of working on a street corner or a shop front they can now scale the approach to massive numbers using the internet. While technology helps to some degree the complete answer can’t be found without addressing the human factor
https://www.securityweek.com/2020-rings-new-era-cyber-attacks-and-its-getting-personal
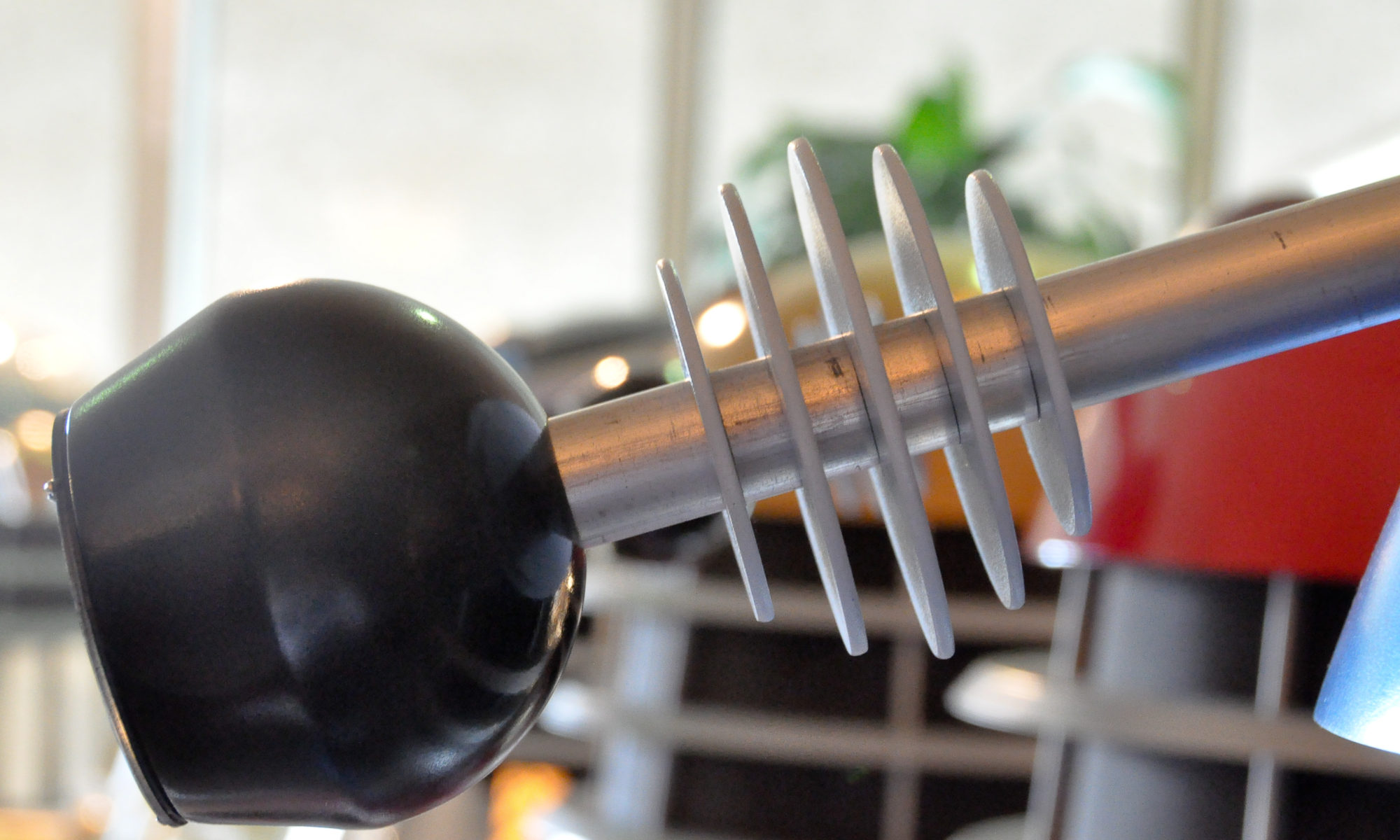
Strange biometric!
Probably never going to be the first choice for a bio-metric identification method!
A breach of a slightly different kind
Well this one is a bit different, and concerning. Device credentials were targeted as opposed to web account credentials.
Not a lot published so far on this and most of the different sources state the same information.
It will be interesting to see where this one ends up
Use technology to fight the good fight….always
Don’t get me wrong here. This is a serious issue and one that would benefit from the application of technology to help the mammoth effort of track and trace required to fight the pandemic. But if we have managed to mobilize the amount of resources we have so far in the response to this, surely we can also mobilize the necessary skills, both technical and policy, to ensure that whatever tracking system we create has the safeguards necessary to protect the rights and privacy of the citizen.
We have the potential capability to deploy a mechanism that would make this crisis and any future ones like it easier to manage and save lives. But this doesn’t mean that we need to create something that has far reaching consequences after the crisis is over.
Like all good applications should be, design the necessary security and privacy safeguards in now, rather than later when it is a problem.
#privacy #infosec #security
Someone buy Zoom a book on Secure Development?
I think there are a couple of lessons here.
Media love to dogpile on a tech company that gets security wrong publicly, and Zoom certainly got it wrong (secure development is not really a new concept guys). That said, I wouldn’t go so far as to call this malware as some articles have. It represents a need for everyone to know the full extent of their supply chain for not only the products and hardware they own, but also the services they consume.
That said, if you are using Zoom right now to easily allow grandma to communicate safely with the grandkids during these times, more power to you. If you are conducting sensitive company meetings over the platform, well…….maybe stop for now?
#infosec #securedevelopment
https://www.nytimes.com/article/zoom-privacy-lessons.html
Do you measure cyber security in securitons?
I recently attended a talk by the head of ADF Information Warfare Division who indicated that he hates using the word cyber, but it does help get him funding.
I have often heard it said and seen programs designed to improve cyber security. But how do we know when that has been achieved? How to you measure cyber security? Is cyber security in metric securitons? Or is that an imperial measure?
A simple business maxim, if you can’t measure it you can’t manage it. Cyber security is no different.
The following from RAND, Measuring Cyber Security and Cyber Resiliancy is an intersesting framework that approaches the matter not just from the inside of the organisation covering the maturity level of the system security, but also from the defensive side covering the maturity level of the defences. Both important attributes to measure to make up your organisations ‘securitons’
https://www.rand.org/pubs/research_reports/RR2703.html
Working at home safely
For organisations that already had remote capabilities, these very different times that we are now in likely represent only an increase in capability rather than new capability.
But for those organisations suddenly thrust into the need to give their employees remote access to their systems and files for the purposes of just staying in business, standing up the necessary technology and processes to enable remote access security can be difficult.
SANS has published a good basic toolkit just for that purpose
https://www.sans.org/security-awareness-training/sans-security-awareness-work-home-deployment-kit
Poking holes in encryption
Yeah, well……we kinda did really.
Don’t get me wrong, I think something needs to be done to provide a balance for genuine law enforcement requirements, but as we have seen with technology related legislation of the last few years, it is generally not very good and not really what was sold to the Australian public (looking at you metadata retention legislation!). If a bad actor truly wants to avoid the impact of this legislation they just use a third party encryption product readily available in their multitudes via Google.
Technology related legislation is necessary but it takes time and it also takes consideration of what type of society we want to create for ourselves. Both of which have yet to surface so far.
Prepare for memetic warfare!
While I doubt we will see a full repeat of the shenanigans experienced in the 2016 US election I believe it will be interesting to see how various groups attempt to weaponise their social media presence.
We are fortunate that our electoral system counteracts some of the outcomes of memetic warfare experienced in influence campaigns seen so far, but you have a very flexible tool with a low barrier to entry for information warfare in the hands of motivated groups. I suspect we will see some activity
Social Media or Information Warfare?
Ok, so it was only 30 million accounts and not 50 million…..that’s ok then!
Interesting conjecture as to who was behind the attack. Further evidence I think that identifies FaceBook as no longer being a social media platform but a tool for Cyber Enabled Information Warfare. Whether you use it illegally like these threat actors have or go in as a legitimate customer and pay the money, it is undeniable the power that this tool can provided beyond sharing cat pictures.
https://www.databreachtoday.com/facebook-clarifies-extent-data-breach-a-11598